Introducing Nextware’s Cumulus SSO Integration
Introducing Nextware’s Cumulus SSO Integration https://www.nextwaretech.com/wp-content/uploads/2015-12-1-Single-Sign-On-SSO-Integration-for-Canto-Cumulus-1024x683.jpg 1024 683 Nextware Technologies Nextware Technologies https://www.nextwaretech.com/wp-content/uploads/2015-12-1-Single-Sign-On-SSO-Integration-for-Canto-Cumulus-1024x683.jpgOur most popular DAM integration, the Nextware Cumulus Single Sign-on (SSO) Integration, allows endusers already logged into their workstations to seamlessly be logged into any of Canto Cumulus’ web interfaces, including Portals, Cumulus Web Client (CWC) and Sites, for Cumulus versions 9.2.x and later. We decided to use PingOne acting as the SAML service provider endpoint, but our integration is flexible to also support other scenarios such as waffle Tomcat request user or AES encrypt / decrypt from Sharepoint and WordPress, to name just two. Soon we will also add support for SAML 2.x for any system.
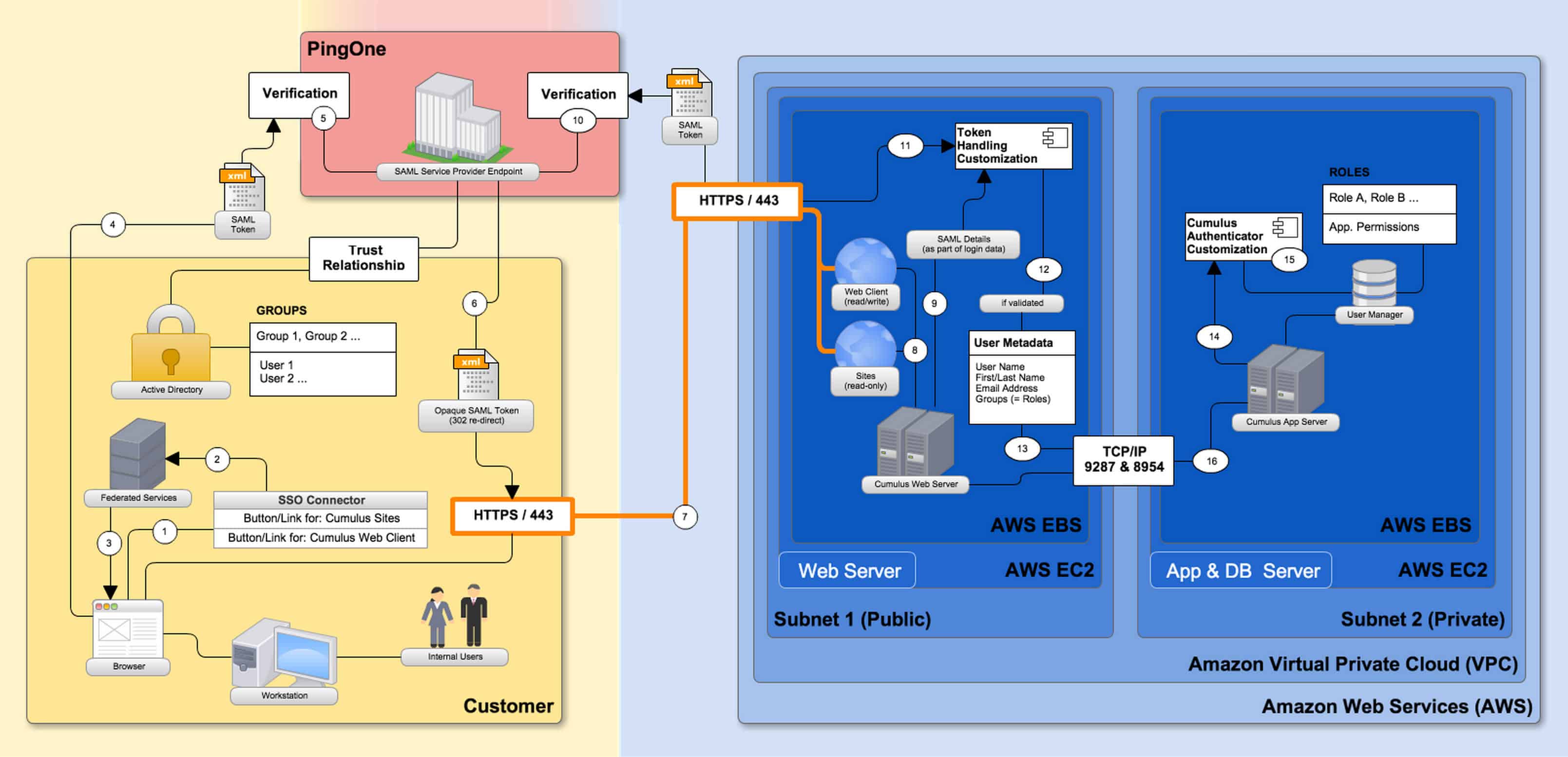
The following diagram illustrates the complete integration in an AWS environment, but any other environment is possible, too. It endusers to simply click on a button or link and immediately be connected to Cumulus web interfaces without having to log in again.
This SSO integration is highly secure, as it validates the user details twice, once customer-side and a second time between Cumulus/AWS and PingOne. Furthermore, it still allows all other, regular Cumulus authentication options to be employed in parallel. That includes built-in users and AD-authenticated users, as the custom SSO Authenticator module is simply added as another Cumulus authentication module, but does not replace the existing Cumulus authentication modules. This gives customers a lot of flexibility to create mixed authentication scenarios. In fact, our particular customer uses all three authentication options:
- Internal users connect via SSO
- External agencies (not pictured in the diagram) connect via an AWS-hosted AD
- Certain technical Cumulus users (like RoboFlow) connect as built-in users
So how does this SSO integration work?
- A SAML token generated by our client’s federated service includes a re-direct URL.
- Upon authentication completion, the return token (incl. all user metadata needed to verify the SAML token) is re-directed to the respective Cumulus web interface.
- This data is transferred to the Cumulus Web Server as part of the login data.
- The Cumulus Web Server connects to the PingOne server to verify the token.
- Once verified, PingOne returns a SAML token with details (valid/not valid).
- The Cumulus Web Server does a “Connect to Cumulus App Server” and posts a XML/JSON structure that the Cumulus App Server parses to authorize the user.
- The Cumulus Server assigns user metadata and matches groups with roles based on the posted XML/JSON.
This only required very few integration parts which can easily be adapted to any future release of Cumulus, including:
- A Cumulus Web Server “Token Handling Customization” that can be used to trigger a “Connect to Cumulus App Server” with PingOne’s SAML token handling.
- A Cumulus App Server “Authenticator Customization” that will understand the XML/JSON structure posted by the Cumulus Web Server.
This integration is extremely flexible and can be adapted to fit additional requirements. If you are interested in this or other DAM customizations and/or integrations, please get in touch with us today.
Pricing
- Base Price: US$ 7,995
- Initial setup and configuration (10 hours @ US$ 200 per hour): $2,000
- Total: US$ 9,995
- Training, Upgrades and Support not included (see below)
System Requirements
- For Canto Cumulus Enterprise solutions only
- Available for Sites, Cumulus Web Client and Portals
- Available for Cumulus 9.2.x and later
Maintenance Options
- Ad-Hoc Maintenance
- Incident Technical Support, Training or Upgrades (to adapt integration to newer versions of Cumulus)
- Cost: $200/hour
- Maintenance Agreement
- 1 year of Technical Support and Free Upgrades, Cost: 36% of Base Price/year = $US 2,878
- This includes:
- Incident Technical Support
- Free Access to the latest version of the Nextware Cumulus SSO Integration (to make it work with the your latest and current version of Cumulus)
- Not included:
- Extra Training
- Professional Services related to upgrades or configurations beyond the initial setup & configuration